This section describes how to delete local users from One Identity Safeguard for Privileged Sessions (SPS).
To delete a local user from SPS
-
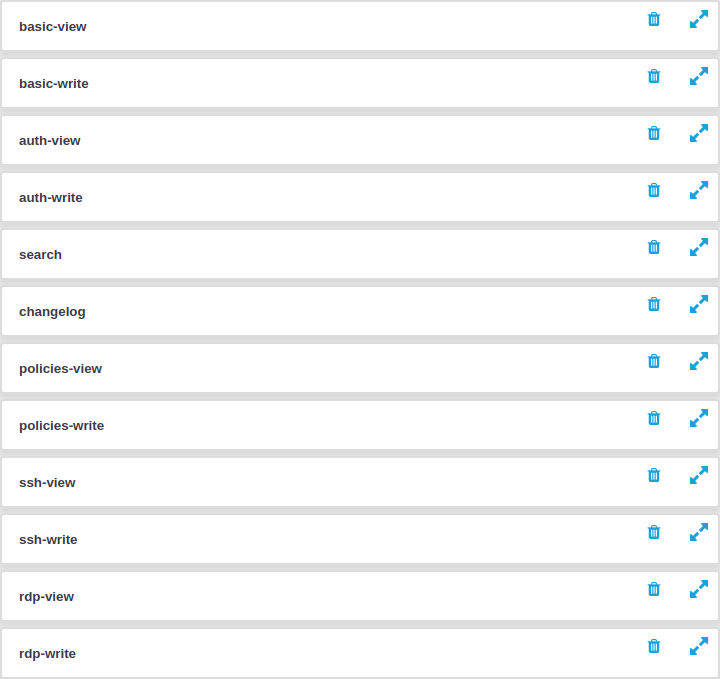
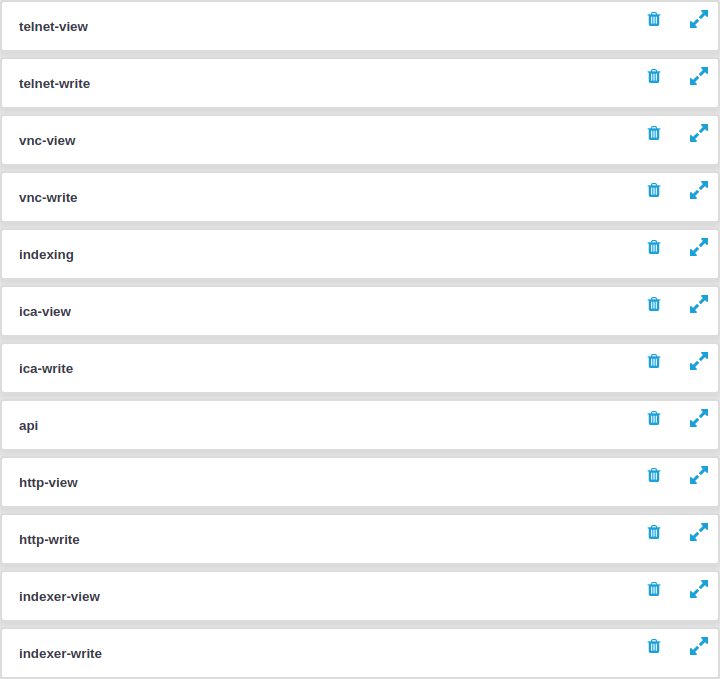
Navigate to Users & Access Control > Local Users.
-
Find the user you want to delete.
-
Click
next to the user, at the right edge of the screen.
-
To save your modifications, click Commit.

 .
.